From Farm to Bryley’s Table
Wilson Farm was founded by Irish immigrants and has been in operation at its present location, Lexington, MA since 1884.
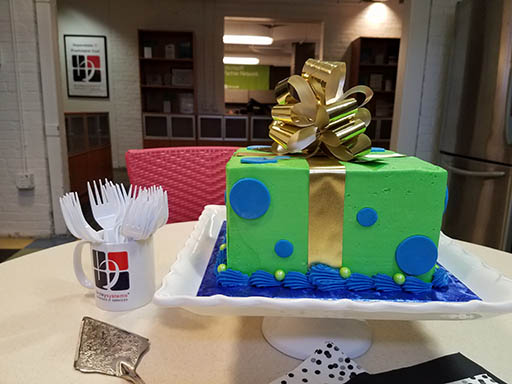
Thank you for the delicious cake!

Wilson Farm was founded by Irish immigrants and has been in operation at its present location, Lexington, MA since 1884.
Thank you for the delicious cake!
A sense of belonging, a sense of community and for businesspeople, a touchpoint for customer service and the ability to market to specific demographics are among social media’s benefits. And like every technology, social media – by which I mean websites that offer sharing tools that allow people to interact (e.g. Instagram, Twitter, SnapChat, Facebook, YouTube) – have their drawbacks.

“We are team-oriented at Bryley Systems,” said Livingstone, “and I look forward to continue working within a collaborative environment, providing excellent services to our clients, as we strategically plan for the future growth of the company.”
In 2008, Mr. Livingstone joined Bryley Systems as part of the technical-services team and has held the positions of senior technician, project manager and director of technical services.
Bryley Systems Inc. is pleased to announce Virginia Livingstone as Director of Technical Services.
“Ms. Livingstone will lead our technical-services team,” states Gavin Livingstone, Bryley’s President, “while expanding and providing the highest-level of service quality and client care.”
Early 2017, Virginia joined Bryley Systems, bringing with her over 20 years’ experience troubleshooting and diagnosing client issues. She is experienced in team leadership, well-versed in server database and network support tools, and possesses strong debugging skills.
Prior to Bryley Systems, Virginia was an IT Automation Engineer for Intel Corporation in Hudson, MA. She holds a degree in Computer Science from Clark University.
“Our Technical Services Department is dedicated every day to answering questions and assisting with our client’s IT needs.” Said Ms. Livingstone. “I am extremely proud and excited to assume this leadership role and pursue future successes.”
National Battery Day is observed on February 18, 2019.
Think on that day about the usefulness of the batteries – and charging some up again, if you like. Recognize, just how important the simple battery is to our way of life. In electricity, a battery is a device consisting of one or more electrochemical cells that convert stored chemical energy into electrical energy. Batteries have become a common power source for many household and industrial applications.
There are two types of batteries: primary batteries (disposable batteries), which are designed to be used once and discarded, and secondary batteries (rechargeable batteries), which are designed to be recharged and used multiple times. Batteries come in many sizes, from miniature cells used to power hearing aids and wristwatches to battery banks the size of rooms that provide standby power for telephone exchanges and computer data centers.
As much as we depend on batteries to help power our daily lives, it’s also our responsibility to recycle them when they reach their end-of-life.
Battery recycling not only prevents potentially hazardous materials in batteries from harming the environment, it can protect against potential fires by keeping batteries out of the garbage and helps conserve our natural resources.
It’s easy and convenient – find a drop-off location near you. Be sure to review guidelines on how to safely prepare your batteries. Help us lead the charge on battery recycling today and every day!
With Valentine’s Day just around the corner, many of us will go online for gifts such as flowers, candy, cute stuffed animals, a book, perhaps a gift card to a store or restaurant – whatever the choice may be, will you be shopping securely? Online shopping is very convenient.
You can click here and there and order whatever product you desire and have it delivered to your front door. You can compare pricing, look for deals, compare products, and it all can be done quickly and in the convenience of your own home, any time, night or day. The downfall? Wherever there is money and users to be found, there are malicious hackers roaming around.
Use familiar web sites. You need to be aware of the safer online shops, like Amazon. One tactic favored by malicious hackers is to set up their own fake shopping websites. Fake websites can either infect you the moment you arrive on them by way of malicious code. However, the most dangerous aspect you should be concerned about is the checkout process. Completing a checkout process will give cybercriminals your most important information: credit card data (including security number), name, and address. This opens you up to credit card fraud or social engineering attacks.
What are some key things to be aware of as you’re shopping? “Sticking with popular brands is as good as any advice when shopping online. Not only do you know what you’re getting by way of quality and price, but you also feel more confident that these well-established names have in place robust security measures.”1
A few things to be aware of:
The old adage “if it seems too good to be true, it probably is,” rings true in this case, and it’s best to steer clear of these sites.
Use Secure Connections. Wi-Fi has some serious limitations in terms of security. Unsecured connections allow hackers to intercept your traffic and see everything you are doing on an online shop. This includes checkout information, passwords, emails, addresses, etc.
Before You Buy Online…
Access secure shopping sites that protect your information. If you want to purchase from a website, make sure it has SSL (secure sockets layer) encryption installed. The site should start with https:// and you should notice the lock symbol is in the address bar at the top.
Update your browser, antivirus and operating system. One of the more frequent causes of malware is unpatched software. Online shoppers are most at risk due to the sensitive information involved. At a minimum, make sure you have an updated browser when you are purchasing online. This will help secure your cookies and cache, while preventing a data leakage. You’ll probably fuss over having to constantly update your software because it can be a time consuming operation, but remember the benefits.
Always be aware of your bank statement. Malicious hackers are typically looking for credit card data, and online shops are the best place for them to get their hands on such information. Often times, companies get hacked and their information falls into the hands of cybercriminals.
For this reason, it’s a good habit to review your bank account and check up on any suspicious activity.
“Don’t wait for your bill to come at the end of the month. Go online regularly and look at electronic statements for your credit card, debit card, and checking accounts. Make sure you don’t see any fraudulent charges, even originating from sites like PayPal. If you do see something wrong, pick up the phone to address the matter quickly. In the case of credit cards, pay the bill only once you know all your charges are accurate. You have 30 days to notify the bank or card issuer of problems.”2
Using a credit card vs. a debit card is safer. Credit cards have additional legal defenses built in that make them safer to purchase online compared to debit cards. With credit cards, you aren’t liable if you are a victim of a fraudulent transaction, so long as you report the fraud in a timely manner. Secondly, credit cards give you leverage when it comes to disputing transactions with a seller. If you pay with a debit card, you can’t get your money back unless the seller agrees to it. With credit cards, the money you paid for a product isn’t counted against you until due process is complete, debit card holders however can only get their money back after this step. Ultimately, banks are much more protective of credit cards since it’s their money on the line, not yours.
Additional tips for safety:
Use antivirus protection. The most frequent tip on how to be safe online is to use a good antivirus tool. It will keep you safe against known malware. ”Before you begin shopping, outfit your phone or tablet with mobile security software. Look for a product that scans apps for viruses and spyware, blocks shady websites, provides lost-device protection and offers automatic updates.”3
Do not purchase from spam or phishing emails. A phishing email with a fake offer for a desirable product is a hard thing to resist for many shoppers, so they make an impulsive decision and click on the “Order Product” or “Buy Now”, and that’s when the malware attack starts. A phishing email is not like a standard email. The cybercriminal simply wants your click, and nothing else. The Unsubscribe button won’t stop the email spam. The best solution in these cases is for you to simply mark the email as spam, this will remove the mail from your inbox and block the sender from sending more spam.
Keep a record of your transactions. If you are a frequent online shopper, it may be difficult to remember from which site you bought a certain product. So, write it down: what you bought, when and from what website. Compare your spending details with the banking records from your online banking account, keep track of which websites you use for shopping and buying stuff online.
Hold on to your receipts and destroy them when you no longer need them. Keep the receipt for your purchase, just in case you need to confirm it again, as well as for warranty and return issues. If you want to get rid of receipt, make sure to destroy it completely, so that any possible identity thief won’t be able to find any information about you.
Don’t give out more private information than you need to. ”In order to shop online you need to provide two types of information: payment information, such as credit card data, and shipping location, which is usually your home or work address. Be suspicious of online shops that ask for information such as: date of birth, social security number or any other similar information. They don’t need it in order to sell you things.”4
Don’t keep too much information on your smartphone. These days, everybody stores a lot of important personal information on their phone, and most of us rarely take the time to secure them. These devices are now much less about calling people, and more about photos, social media, etc. Increasingly, people shop online using their smartphone, but this carries its own risks. Fake online shops can infect your smartphone with malware, and then have access to information such as phone numbers, notes, photos, and even app contents. Be careful what information you store on your smartphone.
“Safer Internet Day is a great reminder that Internet security is something that needs constant vigilance. It’s also a great reminder that a lot of bad things can happen on the Internet if you don’t properly take precautions against them. With that in mind, be sure to have a safe and happy Safer Internet Day.”5
References:
1 welivesecurity.com – ESET Security Forum
2 pcmag.com
3 Smart Mobile Tips For Online Shopping – TrendMicro
4 bettermoneyhabits.bankofamerica.com
5 “Safer Internet Day” – holidayscalendar.com
staysafeonline.org – Powered by National Cyber Security Alliance
americanbar.org – American Bar Association
foxnews.com
usatoday.com
In 2017 we saw cybercriminals adopt a whole new approach to generating value from malware. Rather than stealing information or encrypting a victim’s files and demanding a ransom, cybercriminals started discretely hijacking computer systems and using them to generate cryptocurrency. In 2018, cryptojacking became one of the most prevalent forms of malware on the internet. The question to ask yourself in 2019 is “can I spot such an attack and, if I can, what do I do about it?”
Just about everything requires a computer these days. When your computer works, it’s great. When a problem arises, the first thing to do is try not to panic.
There are many different things that could cause a problem with your computer. No matter what’s causing the issue, troubleshooting will always be a process of trial and error. You may find yourself trying a few different approaches before you can find a solution. Some issues are easy to fix and others may require the help from a professional, but if you decide to try to tackle it on your own here are a few tips.
Process of Elimination. If you’re having an issue with your computer, you may be able to find out what’s wrong using the process of elimination. This means you’ll make a list of things that could be causing the problem and then test them out one by one to eliminate them. Once you’ve identified the source of your computer issue, it will be easier to find a solution.
This is just one example of an issue you might encounter while using a computer. You are trying to print, but the printer won’t print. You have some ideas about what could be causing this, so you go through them one by one to see if you can eliminate any possible causes.
Simple solutions to common problems.
Sometimes, problems can be fixed using simple troubleshooting techniques, like closing and reopening the program. It’s important to try these techniques before resorting to more extreme measures. If the problem still isn’t fixed, you can try other troubleshooting methods.
Power button will not start computer.
An application is running slowly.
An application is frozen.
Sometimes an application may become frozen. When this happens, you won’t be able to close the window or click any buttons within the application.
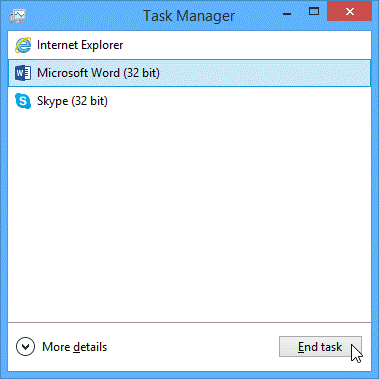
Slow Performance.
Virus.
A virus is a malicious computer program that is designed to interfere with the operation of a computer program or destroy computer programs. They occur in various forms and they normally attack computers from various sources such as infected external memory modules, fake software, or the internet.
The computer is frozen.
Sometimes your computer may become completely unresponsive, or frozen. When this happens, you won’t be able to click anywhere on the screen, open or close applications, or access shut-down options.
Mouse or Keyboard Stops Working.
Blue Screen of Death (BSOD).
This is a very common computer problem especially if you have installed sketchy or buggy software. The most important question to ask yourself is what did I just do before the device stopped working? If you installed a new piece of software, plugged in to new hardware, downloaded custom drivers, installed a Windows update, or changed settings, this could be the cause. Depending on what you just did, the repair may depend on that change.
No Sound.
Blank Screen.
If you don’t find a solution to your problem, you may need to ask a family member or friend for assistance. You can always search the Web, look for a YouTube video or a chat line. Keep in mind that some computer problems have simple solutions, although it may take some time to find them.
For more complex problems, more in-depth solutions may be required, such as reformatting your hard drive or reinstalling your operating system. Call us at 978-562-6077, or email us at ITExperts@Bryley.com. We are here to help.
It was the night before Christmas and we were all here
Checking e-mails, closing tickets and wishing each other good cheer
Festivities full of food and presents to swap
Here for our clients because “Bryley Rocks!”
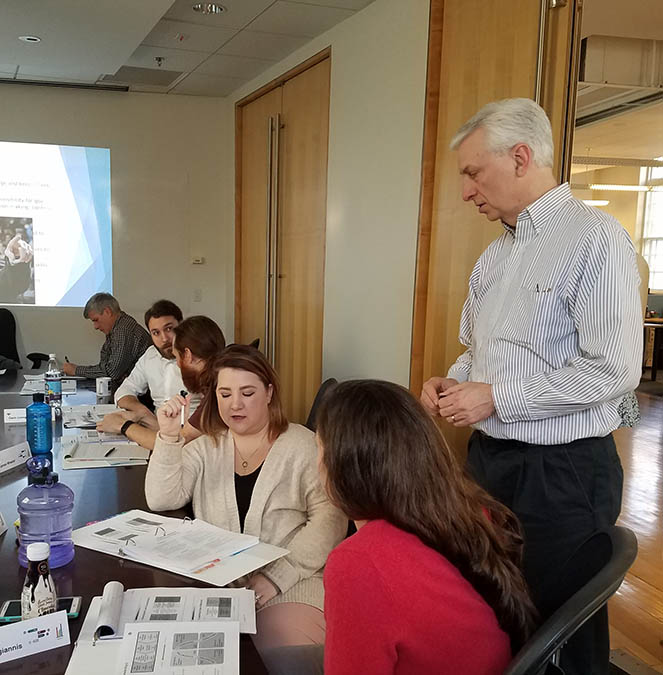
We are excited about the opportunity this training creates for Bryley systems. So far the focus has been on effective communication and leadership skills. As we move further into 2019, the training program shall become more targeted, focusing on individual departments and the unique skill sets required by Bryley personnel to be effective in their specific roles.

In 2017, companies completing grants added jobs at a rate of 8.2%, as opposed to the statewide average 3.1%, and the New England average 2.7%.
This project is funded by a Workforce Training Fund grant from the Commonwealth of Massachusetts, Executive Office of Labor and Workforce Development. The grant program is administered by Commonwealth Corporation.

