At Bryley Systems, we specialize in providing comprehensive IT risk assessment in Clinton, designed to identify and address potential security threats within your organization. Our team of experts conducts a thorough evaluation of your IT infrastructure, including networks, servers, software, and workflows, to pinpoint vulnerabilities that could expose your business to cyberattacks, data breaches, or downtime. We recognize the unique challenges faced by businesses in Clinton and customize our assessments to ensure they address your specific needs. Whether you’re a small business or an established enterprise, our IT risk assessments are tailored to safeguard your operations and help you make informed decisions about your IT security.
Our IT risk assessment services go beyond identifying risks; we provide actionable insights and practical recommendations to improve your security posture. We help you implement robust risk mitigation strategies, ensure compliance with relevant regulations, and bolster your disaster recovery plans.
What is IT Risk Assessment?
IT risk assessment in Clinton is a vital process that helps businesses identify, evaluate, and address potential vulnerabilities in their IT systems and infrastructure. This comprehensive assessment focuses on analyzing your company’s networks, hardware, software, and policies to uncover risks such as cyberattacks, data breaches, compliance failures, and system malfunctions. By conducting a thorough IT risk assessment, businesses in Clinton can proactively secure their sensitive data, ensure compliance with industry regulations, and prevent costly disruptions. At Bryley Systems, our expert team provides tailored IT risk assessments designed to identify critical vulnerabilities in your environment and offer actionable insights to strengthen your security posture. With our IT risk assessment services, you can mitigate risks, enhance your cybersecurity strategy, and safeguard your operations, ensuring your IT infrastructure remains resilient against evolving threats.
A Bryley Risk Assessment: The First Step to Stronger Security
A Bryley Risk Assessment provides a thorough analysis of your existing data environment, identifying potential vulnerabilities and risks. This assessment creates a comprehensive roadmap for improving security and reducing risks in the future. With IT Risk Assessment in Clinton by Bryley Systems, businesses gain valuable insights into their infrastructure, ensuring compliance with industry standards and strengthening data protection. Our team helps implement security measures that enhance your organization’s resilience and long-term security.
Types of IT Risks That Can Impact Businesses in Clinton
When conducting an IT Risk Assessment in Clinton, businesses need to consider various types of risks that can affect their operations. These include:
1. Cybersecurity Risks
- Data Breaches: Unauthorized access to sensitive information that can result in financial loss and reputation damage.
- Hacking: Malicious attempts to gain control over systems, often leading to theft of intellectual property or operational disruption.
- Phishing Attacks: Deceptive tactics used to obtain sensitive data such as login credentials, which can compromise security.
2. System Failures and Downtime Risks
- Hardware Failures: Breakdown of physical components like servers or hard drives that can halt business operations.
- Software Failures: Bugs, glitches, or outdated software that can cause disruptions in business continuity.
- Network Failures: Loss of connectivity or performance issues that impede communication and productivity.
3. Compliance and Regulatory Risks
- Data Protection Regulations: Failure to comply with industry standards such as GDPR, HIPAA, or CMMC can lead to hefty fines.
- Legal Liabilities: Inadequate data security measures can expose businesses to lawsuits and legal actions.
- Audits and Inspections: Non-compliance can lead to failed audits, loss of contracts, or penalties from regulatory bodies.
4. Insider Threats and Human Error Risks
- Malicious Insider Threats: Employees or contractors with malicious intent who compromise security for personal gain.
- Human Error: Simple mistakes such as sending emails to the wrong recipients, which can result in data leaks or system breaches.
- Lack of Training: Insufficient knowledge about security protocols can lead to accidental breaches or misuse of sensitive data.
Essential IT Risk Assessment Tools and Methodologies for Effective Security
Bryley Systems offers a comprehensive IT Risk Assessment in Clinton using a combination of tools and methodologies designed to address potential vulnerabilities and ensure security.
Key components include:
- Vulnerability Scanners
- Penetration Testing
- Risk Management Frameworks
- NIST SP800-30 Standard
- Data Integrity & Business Continuity Evaluation
- Tailored Solutions
- Compliance Assurance
With these tools and methodologies, Bryley Systems offers a thorough IT Risk Assessment in Clinton, helping businesses secure their infrastructure and stay compliant.
Bryley IT Risk Assessment will:
An IT Risk Assessment in Clinton is a vital tool for enhancing the security posture of businesses. By identifying vulnerabilities and evaluating potential threats, organizations can implement effective strategies to safeguard their assets and ensure business continuity.
Our assessment process includes:
- Establishing a Risk Baseline
We assess your current IT infrastructure to establish a baseline for potential risks. - Identifying Areas of Risk
We review your administrative, physical, and technical environments to pinpoint risks. - Documenting Sensitive Data and Systems
Key data, systems, third-party connections, and business processes are documented to protect critical assets. - Compliance with Regulatory Frameworks
We ensure your risk assessment aligns with industry standards, like NIST compliance or CMMC. - Developing a Risk Reduction Roadmap
A tailored roadmap outlines actionable steps to reduce risks, available in one-, two-, or three-year plans.
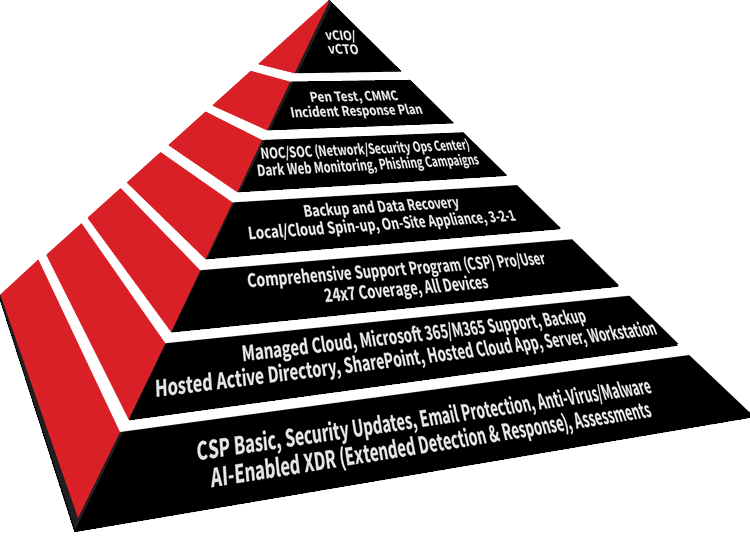
Based on NIST SP800-30
Bryley Systems offers a comprehensive IT Risk Assessment in Clinton, built on the globally-recognized NIST SP800-30 framework. This foundational component of our Business Continuity Pyramid provides a detailed evaluation of your organization’s information security risks.
Our assessment process helps businesses:
- Identify and Evaluate Risks
We identify potential security risks and determine their likelihood of occurring, along with the potential impact on your organization. - Develop Mitigation Strategies
Based on the assessment, we provide a comprehensive risk mitigation strategy to address identified vulnerabilities. - Align with Industry Standards
Our risk assessment follows the NIST SP800-30 standard, ensuring your organization adheres to internationally accepted guidelines for IT security.
Bryley Risk Assessment At-A-Glance
Bryley Systems offers comprehensive IT Risk Assessment in Clinton, an essential service for businesses aiming to safeguard their data and maintain robust security measures. Our risk assessments are based on the globally-recognized NIST SP800-30 standard, which helps ensure your IT infrastructure is aligned with best practices and regulatory requirements. Key aspects of our assessment include:
- Confidentiality, Integrity, and Availability: We focus on protecting the core elements of your data to ensure it remains secure and accessible when needed.
- Regulatory Compliance: Our IT risk assessment helps you achieve compliance with commercial, organizational, and industry-specific standards such as NIST and CMMC.
- Risk Identification and Mitigation: We identify potential vulnerabilities within your technical, physical, and administrative environments and develop actionable strategies to reduce risks.
- Comprehensive Evaluation: The assessment process includes evaluating existing security controls, determining the likelihood and impact of risks, and recommending improvements.
- Actionable Roadmap: Based on the findings, we create a customized risk mitigation plan to improve security, enhance operational efficiency, and ensure business continuity over one, two, or three years.
Secure Your Business with IT Risk Assessment Services from Bryley Systems in Clinton
For businesses in Clinton, safeguarding sensitive data and ensuring compliance with industry regulations is essential. With Bryley Systems as your trusted provider of IT Risk Assessment in Clinton, you can take proactive steps to identify vulnerabilities, mitigate risks, and enhance your overall cybersecurity strategy. Our team of experienced professionals works closely with your organization to assess potential threats, prioritize risks, and create a customized roadmap for improving security and compliance. By choosing Bryley Systems, you are ensuring that your business is prepared to face evolving cybersecurity challenges while maintaining operational continuity. Don’t wait for a breach to happen—contact us today to schedule a thorough IT risk assessment and protect your business from potential risks.
Imagine using an MSP that isn’t Bryley Systems ... the only better MSP would be one from a technologically-superior species from another galaxy. –RM, Central Mass manufacturer
Don't settle
Call our managed IT services department at (978) 547-7221 or fill out this form to set up a no-obligation, introductory call.




Central MA Office
200 Union Street Clinton, MA 01510

Existing Customers

Sales Inquiries

© Copyright 2025 Bryley Systems Inc. All Rights Reserved. Website in partnership with Tech Pro Marketing. | Privacy Policy | Accessibility Statement




